ISO/IEC 27001 helps organizations prove that they have implemented best practices in their security and data protection programs. Office 365 has been verified to meet the rigorous set of physical, logical, process, and management controls defined by ISO 27001:2013. This also includes ISO 27018 Privacy controls in the most recent audit. Although an ISO 27001 certification is not mandatory. While working towards it can help you get ready to meet data governance requirements for your customers, partners, employees, and similar acts, laws, regulations, and standards. Similarly, most of these requirements share a common goal: the protection of information and assets.
Why SECLINQ Services
SECLINQ has been at the forefront of cyber security and cyber threat intelligence since 2021. Our incident responders are on the frontlines of the most complex breaches worldwide. We have a deep understanding of threat actors and their rapidly changing tactics, techniques, and procedures (TTPs) by leveraging our combined adversary, machine, and victim intelligence sources.
Overview
With the transition to the cloud, there is a notable rise in security incidents involving cloud platforms and services. Microsoft 365 is highly targeted due to its popularity and valuable hosted data. While compromising Microsoft 365 tenants allows attackers to remotely access sensitive data in the cloud without having to penetrate the corporate perimeter. Threat actors can access Microsoft 365 tenants by exploiting or compromising:
- Weak or legacy authentication mechanisms
- Security controls that have not been optimally configured
- Accounts with privileged access levels
- Accounts with weak passwords or those that do not require multifactor authentication
Recognize and Reduce Risk in Microsoft 365
The SECLINQ Security Assessment for Microsoft 365 was developed based on extensive experience responding to incidents where threat actors have compromised and gained access to an organization’s Microsoft 365 tenant. By proactively reviewing and mitigating common misconfigurations, process weaknesses, and exploitation methods, organizations can reduce overall risk and ensure optimized protection and visibility for events occurring within a Microsoft 365.
The foundation of this assessment includes both the short-term containment and longer-term remediation security controls and configurations required to eradicate attackers from a tenant.
Our Approach
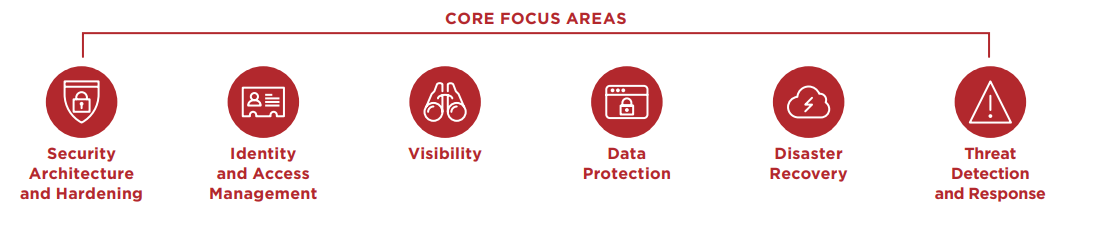
This SECLINQ security assessment evaluates common Microsoft 365 authentication platforms and access controls across six core focus areas:
- Security architecture and hardening
- Data protection
- Identity and access management
- Disaster recovery
- Visibility
- Threat detection and response
Assessment Duration
The Microsoft 365 security assessment typically takes three weeks, consisting of four phases. SECLINQ consultants perform the following activities:
1: Documentation Review
Includes an offsite review of migration strategies, email design and architecture documentation, hardening documentation, logging standards, and Mobile Device Management (MDM) configurations as they relate to accessing a Microsoft 365 tenant.
2: Remote Workshop
A series of remote workshops for each core focus area in collaboration with key client stakeholders.
3: Configuration Review
A thorough configuration review of the Microsoft 365 tenant to ensure that security configurations are optimized in accordance with hardening, security, and protective guidance.
4: Reporting
A report that details practical technical recommendations to harden the Microsoft 365 tenant, enhance visibility and detection as well as improve processes to reduce the risk of compromise for the cloud tenant and related infrastructure.
SECLINQ itself supports ISO 27001 certification and has been able to meet many of the ISO 27001 requirements. Therefore we have been able to do things like:
- Automatically apply data classification to data at rest and any newly-created document based on sensitivity, document/information type, and retention period
- Identify non-conformities in the Incident Management Center
- Automate third-party vendor risk assessments
- Evaluate security in contracts using Impact Assessments
Deliverables
At the completion of the engagement, in addition, SECLINQ experts provide a detailed report that includes:
- A snapshot of the existing Microsoft 365 tenant security configuration.
- Specific Microsoft 365 security best practices to align with current configurations as well as operational processes.
- Practical recommendations for enhancing visibility as well as detection.
- Prioritized and detailed recommendations for further hardening the security posture of the Microsoft 365 tenant.
If you’re just beginning your ISO 27001 certification journey or are performing your periodic ISO 27001 review and need a centralized solution to help you with automating some of the ISO requirements. So, consider SECLINQ’s compliance services and feel free to contact us for more information.